CIPPlanner is built with security at its core to protect the data, users, and workflows that support complex capital improvement programs. Our platform is designed to safeguard sensitive financial, project, and contract information while enabling secure collaboration across departments, agencies, and external partners.
From planning through delivery, CIPPlanner embeds security, privacy, and governance controls directly into the platform, so your teams can focus on decision-making, accountability, and delivery with confidence.
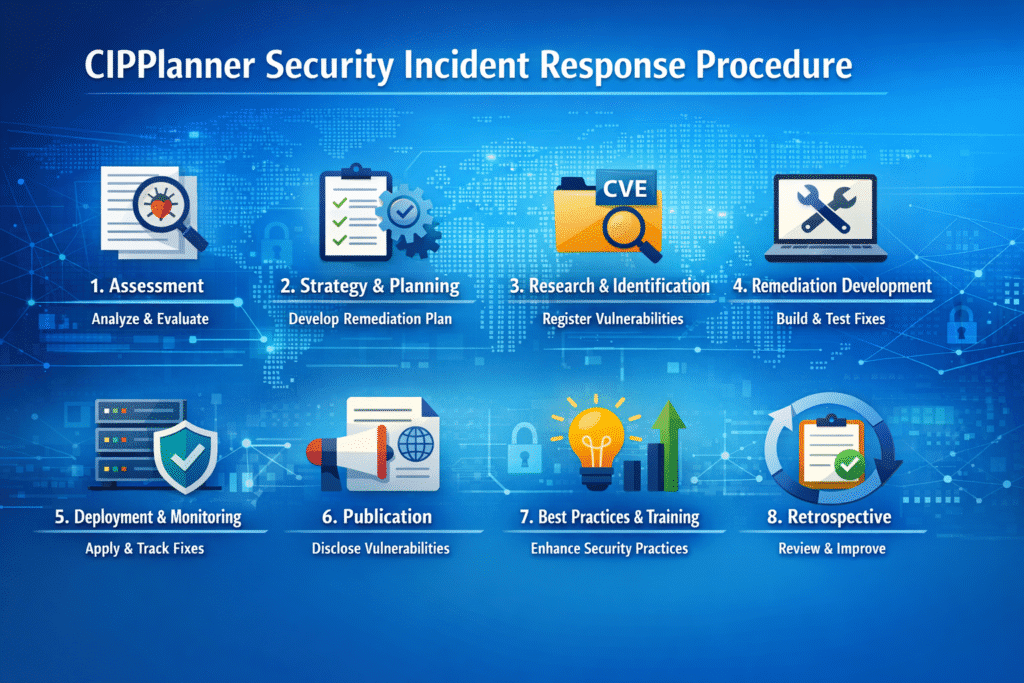
At CIPPlanner, the security of our clients’ applications and data is our highest priority. This Security Incident Response Operating Procedure outlines how CIPPlanner identifies, assesses, remediates, and communicates software security vulnerabilities. The procedure has been developed and executed in response to security vulnerabilities reported by CIPPlanner through MITRE to the Common Vulnerabilities and Exposures (CVE) database.
The primary objective of CIPPlanner’s Security Incident Response Operating Procedure is to minimize the impact of security incidents, contain identified threats, and restore normal operations as quickly and safely as possible.
CIPPlanner recognizes its fiduciary responsibility to:
Identify and track known software vulnerabilities
Communicate transparently with clients and stakeholders
Actively collaborate with customers to help secure their systems
To support transparency and responsible disclosure, CIPPlanner registers discovered software vulnerabilities in the Common Vulnerabilities and Exposures (CVE) database. This ensures that identified risks are documented, traceable, and accessible to both clients and the broader cybersecurity community.
While vulnerability management is critical, CIPPlanner acknowledges that cybersecurity risk management also encompasses broader considerations, including policies, best practices, and organizational capacity-building, particularly as it relates to human resources and operational readiness.
CIPPlanner follows an eight-step, iterative process to achieve enterprise-wide cybersecurity objectives and continuously strengthen platform security.
- Assessment
- Strategy & Planning
- Research & Identification
- Remediation Development
- Deployment & Monitoring
- Publication
- Best Practices & Capacity Building
- Retrospective
Upon discovery of a software vulnerability, CIPPlanner initiates a collaborative assessment process involving cross-functional and inter-departmental teams to clarify and evaluate the issue.
This assessment includes analysis of:
Relevant software components
Methods used by attackers to exploit vulnerabilities
Risks associated with successful exploitation
Severity ratings (e.g., CVSS 4.0)
Impacted CIPAce™ co-existing codebases
During this phase, CIPPlanner evaluates potential contributing factors, including whether vulnerabilities stem from opportunities to enhance development methodologies or engineering practices.
With a comprehensive understanding of identified vulnerabilities, CIPPlanner develops remediation strategies on a customer-by-customer and installation-by-installation basis.
Planning considerations include:
Core system functions (e.g., authentication, user management)
Installed software versions
Custom configurations and integrations
Service delivery models (SaaS or On-Premise)
User populations (internal teams, external vendors)
Embedded third-party software components
This ensures remediation efforts align with each customer’s technical and operational environment.
Discovered vulnerabilities are formally registered in the CVE database, which assigns a unique identifier to known security vulnerabilities in publicly released software.
CIPPlanner’s CVE submission process includes:
Research to confirm whether the vulnerability is newly identified
Documentation and distribution of CVE submission details to stakeholders, including:
CIPPlanner cybersecurity teams
Account and project teams
CIPAce™ customers
Cybersecurity vendors
Important Note:
CVE submissions do not include customer-identifying information. Vulnerabilities are initially submitted under a Private status, allowing CIPPlanner to plan and deploy remediation efforts before public disclosure. Submissions may be updated as new information becomes available.
Where appropriate, research may extend to regulatory environments, infrastructure and IT sectors, and other authoritative resources to enhance remediation efforts and contribute to broader cybersecurity awareness.
This phase focuses on developing effective remediations for identified vulnerabilities, which may include:
Software enhancements or patches
Policy updates
Best practice improvements
CIPPlanner’s technical teams develop, test, and validate remediations across affected CIPAce™ codebases to ensure effectiveness and stability.
CIPPlanner deploys tested remediations in a controlled and orderly manner across applicable environments.
Deployment considerations include:
Service delivery model (SaaS vs. On-Premise)
Customer preference for CIPPlanner-led installation or self-managed deployment
Internal customer operating procedures
For customers opting to manage installations independently, CIPPlanner provides secure download links, patch details, and system requirements. CIPPlanner collaborates with customers to monitor successful implementation and resolution.
CIPPlanner is committed to transparent communication with customers, partners, regulatory bodies, and other stakeholders.
After confirming that all outstanding customer production environments are secured, CIPPlanner:
Publishes a detailed article describing the vulnerabilities and assigned CVE IDs
Notifies the CVE operator (MITRE) of the publication URLs
Supports the transition of CVE records to Public status
Notifies customers upon completion of disclosure
Important Note:
Public disclosure does not occur until all known customer safety concerns have been addressed.
CIPPlanner continuously evaluates and strengthens its cybersecurity posture through:
Policy and procedure enhancements
Improved internal and external collaboration
Expanded communication practices
Organizational capacity-building initiatives
These efforts support proactive and reactive cybersecurity resilience across the platform.
The final step focuses on learning and continuous improvement.
Activities include:
Ongoing software vulnerability testing
Regular third-party penetration testing of CIPAce™
Evaluation of lessons learned from non-software remediation efforts
Insights gained during this phase inform future incident response planning and platform enhancements.
Contact
For questions related to this policy or CIPPlanner’s security practices, please contact:
CNAs (CVE Numbering Authorities) are vendor, researcher, open source, CERT, hosted service, bug bounty provider, and consortium organizations authorized by the CVE Program to assign CVE IDs to vulnerabilities. For further information on CVE, please visit CVE Website.

